If you are using this switch in a highly sensitive network that needs to be very secure, then you might want to consider enabling public key authentication for your SSH connection. Actually, for maximum security, you can enable a username/password and public key authentication for access to your switch. In this article, I’ll show you how to enable public key authentication on an SG300 Cisco switch and how to generate the public and private key pairs using puTTYGen. I’ll then show you how to login using the new keys. In addition, I’ll show you how to configure it so that you can either use just the key to login or force the user to type in a username/password along with using the private key. Note: Before you get started on this tutorial, make sure you have already enabled the SSH service on the switch, which I mentioned in my previous article linked above.
Enable SSH User Authentication by Public Key
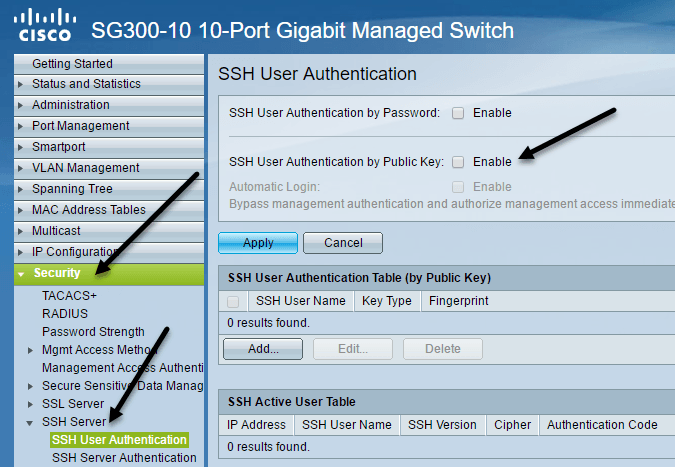
Overall, the process for getting public key authentication to work for SSH is straightforward. In my example, I’ll show you how to enable the features using the web-based GUI. I tried to use the CLI interface to enable public key authentication, but it would not accept the format for my private RSA key. Once I get that working, I’ll update this post with the CLI commands that will accomplish what we will do through the GUI for now. First, click on Security, then SSH Server and finally SSH User Authentication.
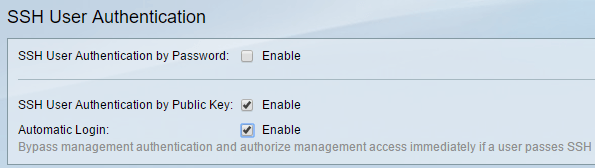
In the right-hand pane, go ahead and check the Enable box next to SSH User Authentication by Public Key. Click the Apply button to save the changes. Don’t check the Enable button next to Automatic login just yet as I’ll explain that further down. Now we have to add a SSH user name. Before we get into adding the user, we first have to generate a public and private key. In this example, we’ll be using puTTYGen, which is a program that comes with puTTY.
Generate Private and Public Keys
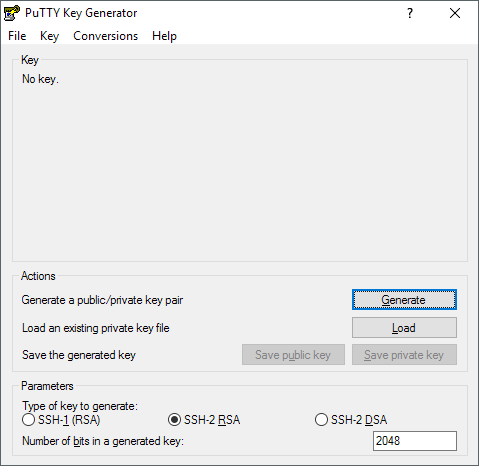
To generate the keys, go ahead and open puTTYGen first. You’ll see a blank screen and you really shouldn’t have to change any of the settings from the defaults shown below.
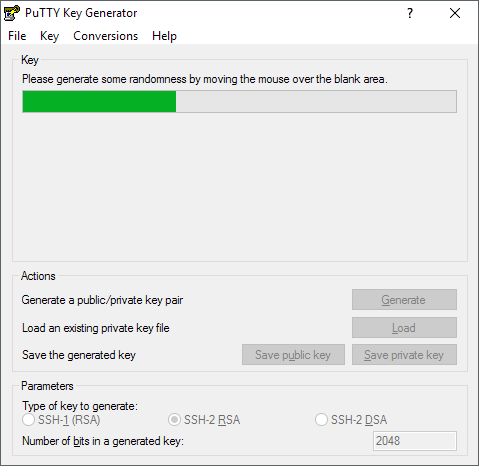
Click on the Generate button and then move your mouse around the blank area until the progress bar go all the way across.
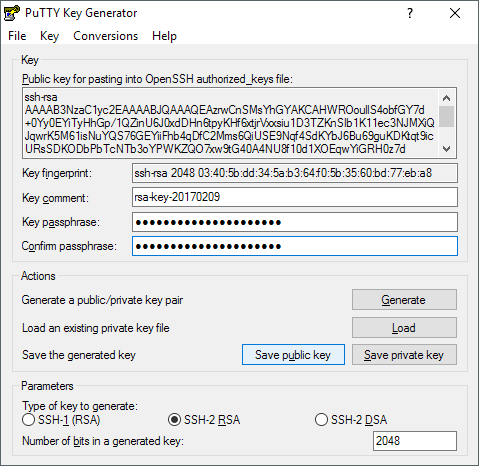
Once the keys have been generated, you need to type in a passphrase, which is basically like a password to unlock the key.
It’s a good idea to use a long passphrase to protect the key from brute-force attacks. Once you have typed in the passphrase twice, you should click the Save public key and Save private key buttons. Make sure these files are saved in a secure location, preferably in an encrypted container of some sort that requires a password to open. Check out my post on using VeraCrypt to create an encrypted volume.
Add User & Key
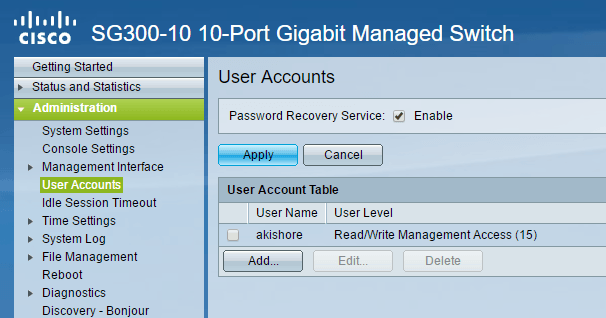
Now back to the SSH User Authentication screen we were on earlier. Here’s where you can choose from two different options. Firstly, go to Administration – User Accounts to see what accounts you currently have for login.
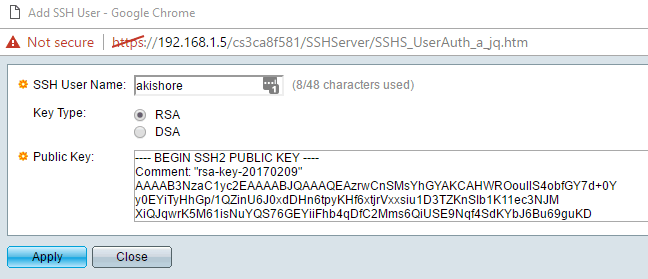
As you can see, I have one account called akishore for accessing my switch. Currently, I can use this account to access the web-based GUI and the CLI. Back on the SSH User Authentication page, the user you need to add to the SSH User Authentication Table (by Public Key) can either be the same as what you have under Administration – User Accounts or different. If you choose the same user name, then you can check the Enable button under Automatic Login and when you go to log into the switch, you’ll simply have to type the username and password for the private key and you’ll be logged in. If you decide to choose a different username here, then you will get a prompt where you have to enter the SSH private key user name and password and then you’ll have to enter your normal username and password (listed under Admin – User Accounts). If you want the extra security, use a different username, otherwise just name it the same as your current one. Click the Add button and you’ll get the Add SSH User window pop up.
Make sure the Key Type is set to RSA and then go ahead and open your public SSH key file that you saved earlier using a program like Notepad. Copy the entire contents and paste it into the Public Key window. Click Apply and then click Close if you get a Success message at the top.
Login Using Private Key
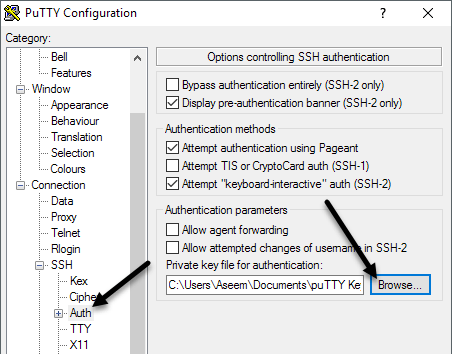
Now all we have to do is login using our private key and password. At this point, when you try to login, you’ll need to enter login credentials twice: once for the private key and once for the normal user account. Once we enable automatic login, you’ll just have to enter the username and password for the private key and you’ll be in. Open puTTY and enter in the IP address of your switch in the Host Name box as usual. However, this time, we’ll need to load up the private key into puTTY also. To do this, expand Connection, then expand SSH and then click on Auth.
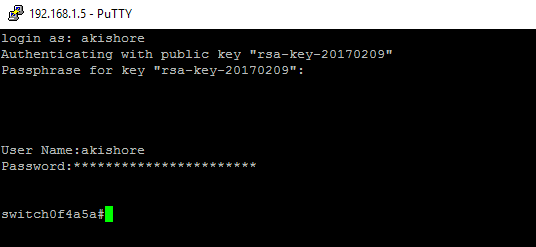
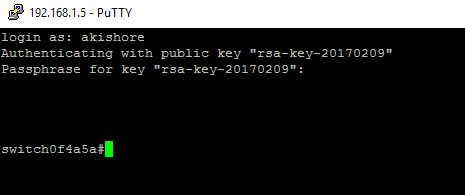
Click on the Browse button under Private key file for authentication and select the private key file you saved out of puTTY earlier. Now click the Open button to connect. The first prompt will be login as and that should be the username you added under SSH users. If you used the same username as your main user account, then it won’t matter.
In my case, I used akishore for both user accounts, but I used different passwords for the private key and for my main user account. If you like, you can make the passwords the same too, but there’s no point in really doing that, especially if you enable automatic login. Now if you don’t want to have to double login to get into the switch, check the Enable box next to Automatic login on the SSH User Authentication page.
When this is enabled, you’ll now just have to type in the credentials for the SSH user and you’ll be logged in.
It’s a bit complicated, but makes sense once you play around with it. Like I mentioned earlier, I’ll also write out the CLI commands once I can get the private key in the proper format. Following the instructions here, accessing your switch via SSH should be a lot more secure now. If you run into problems or have questions, post in the comments. Enjoy!